The National Security Agency (NSA), the Cybersecurity and Infrastructure Security Agency (CISA), and the Federal Bureau of Investigation (FBI) jointly released a Cybersecurity Advisory, “Russian SVR Targets U.S. and Allied Networks,” today to expose ongoing Russian Foreign Intelligence Service (SVR) exploitation of five publicly known vulnerabilities. This advisory is being released alongside the U.S. government’s formal attribution of the SolarWinds supply chain compromise and related cyber espionage campaign. We are publishing this product to highlight additional tactics, techniques, and procedures being used by SVR so that network defenders can take action to mitigate against them.
Mitigation against these vulnerabilities is critically important as U.S. and allied networks are constantly scanned, targeted, and exploited by Russian state-sponsored cyber actors. In addition to compromising the SolarWinds Orion software supply chain, recent SVR activities include targeting COVID-19 research facilities via WellMess malware and targeting networks through the VMware vulnerability disclosed by NSA. This was highlighted in NSA’s Cybersecurity Advisory, “Russian State-Sponsored Actors Exploiting Vulnerability in Workspace ONE Access Using Compromised Credentials.”
NSA, CISA, and FBI strongly encourage all cybersecurity stakeholders to check their networks for indicators of compromise related to all five vulnerabilities and the techniques detailed in the advisory and to urgently implement associated mitigations. NSA, CISA, and FBI also recognize all partners in the private and public sectors for comprehensive and collaborative efforts to respond to recent Russian activity in cyberspace.
NSA encourages its customers to mitigate against the following publicly known vulnerabilities:
- CVE-2018-13379 Fortinet FortiGate VPN
- CVE-2019-9670 Synacor Zimbra Collaboration Suite
- CVE-2019-11510 Pulse Secure Pulse Connect Secure VPN
- CVE-2019-19781 Citrix Application Delivery Controller and Gateway
- CVE-2020-4006 VMware Workspace ONE Access
For more information, review the advisory or visit NSA.gov/cybersecurity-guidance.
View the infographic on understanding the threat and how to take action.
Fachartikel

RC4-Deaktivierung – so müssen Sie jetzt handeln

Plattform-Engineering im Wandel: Was KI-Agenten wirklich verändern

KI-Agenten im Visier: Wie versteckte Web-Befehle autonome Systeme manipulieren

Island und AWS Security Hub: Kontrollierte KI-Nutzung und sicheres Surfen im Unternehmensumfeld

Wie das iOS-Exploit-Kit Coruna zum Werkzeug staatlicher und krimineller Akteure wurde
Studien
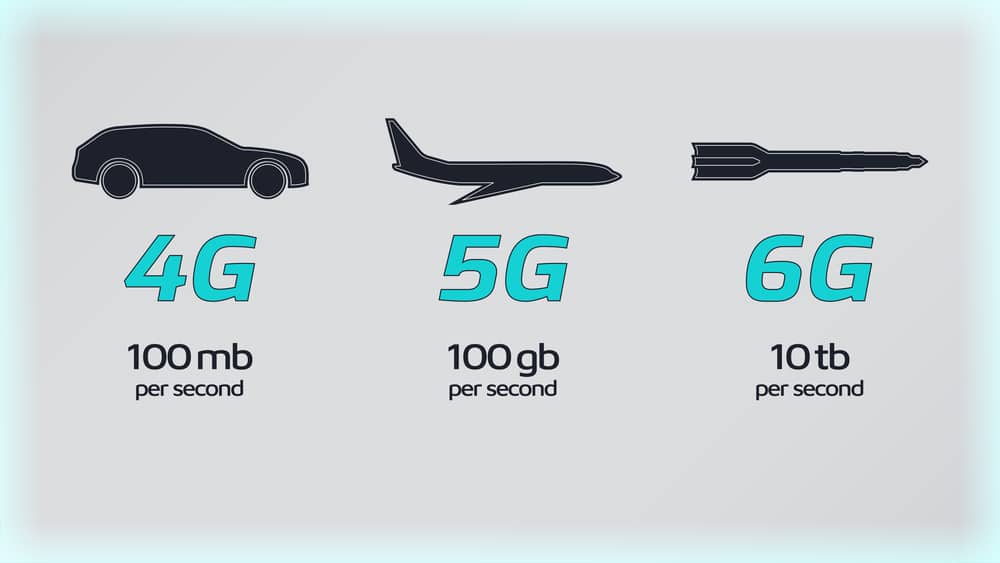
Sieben Regierungen einigen sich auf 6G-Sicherheitsrahmen

Lieferkettenkollaps und Internetausfall: Unternehmen rechnen mit dem Unwahrscheinlichen

KI als Werkzeug für schnelle, kostengünstige Cyberangriffe

KI beschleunigt Cyberangriffe: IBM X-Force warnt vor wachsenden Schwachstellen in Unternehmen
Finanzsektor unterschätzt Cyber-Risiken: Studie offenbart strukturelle Defizite in der IT-Sicherheit
Whitepaper

Cloudflare Threat Report 2026: Ransomware beginnt mit dem Login – KI und Botnetze treiben die Industrialisierung von Cyberangriffen
EBA-Folgebericht: Fortschritte bei IKT-Risikoaufsicht unter DORA – weitere Harmonisierung nötig

Böswillige KI-Nutzung erkennen und verhindern: Anthropics neuer Bedrohungsbericht mit Fallstudien

Third Party Risk Management – auch das Procurement benötigt technische Unterstützung

EU-Toolbox für IKT-Lieferkettensicherheit: Gemeinsamer Rahmen zur Risikominderung
Hamsterrad-Rebell
Sicherer Remote-Zugriff (SRA) für Operational Technology (OT) und industrielle Steuerungs- und Produktionssysteme (ICS) – Teil 2
Incident Response Retainer – worauf sollte man achten?

KI‑basierte E‑Mail‑Angriffe: Einfach gestartet, kaum zu stoppen

NIS2: „Zum Glück gezwungen“ – mit OKR-basiertem Vorgehen zum nachhaltigen Erfolg