The Council today decided to prolong the framework for restrictive measures against cyber-attacks threatening the EU or its member states for another year, until 18 May 2022.
This framework allows the EU to impose targeted restrictive measures on persons or entities involved in cyber-attacks which cause a significant impact, and constitute an external threat to the EU or its member states. Restrictive measures can also be imposed in response to cyber-attacks against third states or international organisations where such measures are considered necessary to achieve the objectives of the Common Foreign and Security Policy (CFSP).
Sanctions currently apply to eight individuals and four entities, and include an asset freeze and a travel ban. Additionally, EU persons and entities are forbidden from making funds available to those listed.
Background
This latest prolongation is part of the EU’s scale up of its resilience and its ability to prevent, discourage, deter and respond to cyber threats and malicious cyber activities in order to safeguard European security and interests.
In June 2017, the EU stepped up its response by establishing a Framework for a Joint EU Diplomatic Response to Malicious Cyber Activities (the „cyber diplomacy toolbox“). The framework allows the EU and its Member States to use all CFSP measures, including restrictive measures if necessary, to prevent, discourage, deter and respond to malicious cyber activities targeting the integrity and security of the EU and its member states.
The EU remains committed to a global, open, stable, peaceful and secure cyberspace and therefore reiterates the need to strengthen international cooperation in order to promote the rules-based order in this area.
- Malicious cyber-attacks: EU sanctions two individuals and one body over 2015 Bundestag hack, press release 22 October 2020
- Council extends cyber sanctions regime until 18 May 2021, press release 14 May 2020
- Council decision concerning restrictive measures against cyber-attacks threatening the Union or its Member States, consolidated text
Fachartikel

KI im SAP-Custom-Code: Sicherheitsrisiken erkennen und gezielt absichern

Zero-Day-Exploits 2025: 90 Schwachstellen, mehr Unternehmensziele, KI als neuer Faktor
Brainworm: Wenn KI-Agenten durch natürliche Sprache zur Waffe werden

Mozilla und Anthropic: Gemeinsame KI-Analyse macht Firefox sicherer

RC4-Deaktivierung – so müssen Sie jetzt handeln
Studien
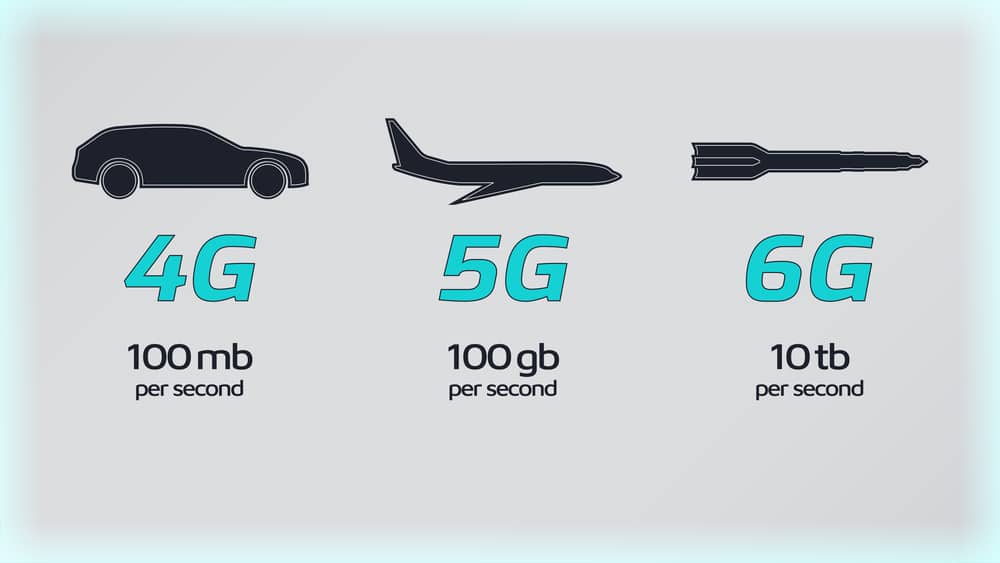
Sieben Regierungen einigen sich auf 6G-Sicherheitsrahmen

Lieferkettenkollaps und Internetausfall: Unternehmen rechnen mit dem Unwahrscheinlichen

KI als Werkzeug für schnelle, kostengünstige Cyberangriffe

KI beschleunigt Cyberangriffe: IBM X-Force warnt vor wachsenden Schwachstellen in Unternehmen
Finanzsektor unterschätzt Cyber-Risiken: Studie offenbart strukturelle Defizite in der IT-Sicherheit
Whitepaper

Cloudflare Threat Report 2026: Ransomware beginnt mit dem Login – KI und Botnetze treiben die Industrialisierung von Cyberangriffen
EBA-Folgebericht: Fortschritte bei IKT-Risikoaufsicht unter DORA – weitere Harmonisierung nötig

Böswillige KI-Nutzung erkennen und verhindern: Anthropics neuer Bedrohungsbericht mit Fallstudien

Third Party Risk Management – auch das Procurement benötigt technische Unterstützung

EU-Toolbox für IKT-Lieferkettensicherheit: Gemeinsamer Rahmen zur Risikominderung
Hamsterrad-Rebell
Sicherer Remote-Zugriff (SRA) für Operational Technology (OT) und industrielle Steuerungs- und Produktionssysteme (ICS) – Teil 2
Incident Response Retainer – worauf sollte man achten?

KI‑basierte E‑Mail‑Angriffe: Einfach gestartet, kaum zu stoppen

NIS2: „Zum Glück gezwungen“ – mit OKR-basiertem Vorgehen zum nachhaltigen Erfolg