
Microsoft hat am Patch Tuesday im August 2025 insgesamt 107 Sicherheitslücken in seinem Produktportfolio geschlossen. Darunter befinden sich 35 kritische Schwachstellen, die eine Remote Code Execution (RCE) ermöglichen – also das Einschleusen und Ausführen von Schadcode aus der Ferne.
Aktuell gibt es keine Hinweise auf aktive Angriffe, die diese Lücken ausnutzen. Dennoch warnen Sicherheitsexperten vor den potenziellen Risiken, insbesondere für Unternehmen mit hybriden oder Cloud-basierten IT-Umgebungen. Eine zeitnahe Installation der Updates wird dringend empfohlen.
Die Patches betreffen ein breites Spektrum an Microsoft-Produkten – von zentralen Windows-Komponenten über Office-Programme und Azure-Dienste bis hin zu Exchange Server und SQL Server. Die Veröffentlichung verdeutlicht erneut, wie beständig Microsoft und die IT-Branche insgesamt gegen immer komplexere Cyberbedrohungen ankämpfen müssen.
Der aktuelle Patch Tuesday zeigt vertraute Angriffsmuster: Häufig treten Use-after-free-Fehler, Heap-Überläufe und mangelhafte Eingabevalidierungen auf – vor allem in älteren Systemkomponenten wie Win32k und den Ancillary Function Drivers.
Besondere Aufmerksamkeit verdient eine behobene Sicherheitslücke in der hybriden Exchange-Server-Bereitstellung (CVE-2025-53786). Microsoft rät Administratoren zudem, die bereits im April 2025 veröffentlichten Hotfixes zur zusätzlichen Absicherung zu installieren.
Für IT-Teams gilt: Updates für internetverbundene Systeme und kritische Infrastrukturen sollten oberste Priorität haben. Privatanwender wiederum sind mit aktivierten automatischen Windows-Updates auf der sicheren Seite.
Zum Stichtag 12. August 2025 liegen Microsoft keine Berichte über aktive Angriffe vor – doch die Erfahrung zeigt, dass veröffentlichte Schwachstellen oft schnell ins Visier von Cyberkriminellen geraten.
This release consists of the following 111 Microsoft CVEs:
| Tag | CVE | Base Score | CVSS Vector | Exploitability | FAQs? | Workarounds? | Mitigations? |
|---|---|---|---|---|---|---|---|
| SQL Server | CVE-2025-24999 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Exchange Server | CVE-2025-25005 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Microsoft Exchange Server | CVE-2025-25006 | 5.3 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:L/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Exchange Server | CVE-2025-25007 | 5.3 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:L/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Exchange Server | CVE-2025-33051 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2025-47954 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Role: Windows Hyper-V | CVE-2025-48807 | 7.5 | CVSS:3.1/AV:L/AC:H/PR:L/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Azure Virtual Machines | CVE-2025-49707 | 7.9 | CVSS:3.1/AV:L/AC:L/PR:H/UI:N/S:C/C:H/I:H/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office SharePoint | CVE-2025-49712 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Edge for Android | CVE-2025-49736 | 4.3 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:L/A:N/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Microsoft Graphics Component | CVE-2025-49743 | 6.7 | CVSS:3.1/AV:L/AC:H/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft Dynamics 365 (on-premises) | CVE-2025-49745 | 5.4 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Role: Windows Hyper-V | CVE-2025-49751 | 6.8 | CVSS:3.1/AV:A/AC:L/PR:L/UI:N/S:C/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Edge for Android | CVE-2025-49755 | 4.3 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:L/A:N/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-49757 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| SQL Server | CVE-2025-49758 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2025-49759 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Kernel | CVE-2025-49761 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Ancillary Function Driver for WinSock | CVE-2025-49762 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Desktop Windows Manager | CVE-2025-50153 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows File Explorer | CVE-2025-50154 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Push Notifications | CVE-2025-50155 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-50156 | 5.7 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-50157 | 5.7 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows NTFS | CVE-2025-50158 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H/E:P/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Remote Access Point-to-Point Protocol (PPP) EAP-TLS | CVE-2025-50159 | 7.3 | CVSS:3.1/AV:L/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-50160 | 8.0 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Win32K – GRFX | CVE-2025-50161 | 7.3 | CVSS:3.1/AV:L/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-50162 | 8.0 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-50163 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-50164 | 8.0 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Microsoft Graphics Component | CVE-2025-50165 | 9.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Distributed Transaction Coordinator | CVE-2025-50166 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Role: Windows Hyper-V | CVE-2025-50167 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Win32K – ICOMP | CVE-2025-50168 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows SMB | CVE-2025-50169 | 7.5 | CVSS:3.1/AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Cloud Files Mini Filter Driver | CVE-2025-50170 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Remote Desktop Server | CVE-2025-50171 | 9.1 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows DirectX | CVE-2025-50172 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Installer | CVE-2025-50173 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Graphics Kernel | CVE-2025-50176 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Message Queuing | CVE-2025-50177 | 8.1 | CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Media | CVE-2025-53131 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Win32K – GRFX | CVE-2025-53132 | 8.0 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows PrintWorkflowUserSvc | CVE-2025-53133 | 7.8 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Ancillary Function Driver for WinSock | CVE-2025-53134 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows DirectX | CVE-2025-53135 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows NT OS Kernel | CVE-2025-53136 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Ancillary Function Driver for WinSock | CVE-2025-53137 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-53138 | 5.7 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Kernel Transaction Manager | CVE-2025-53140 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Ancillary Function Driver for WinSock | CVE-2025-53141 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Brokering File System | CVE-2025-53142 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Message Queuing | CVE-2025-53143 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Message Queuing | CVE-2025-53144 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Message Queuing | CVE-2025-53145 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Ancillary Function Driver for WinSock | CVE-2025-53147 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-53148 | 5.7 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Kernel Streaming WOW Thunk Service Driver | CVE-2025-53149 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Kernel | CVE-2025-53151 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Desktop Windows Manager | CVE-2025-53152 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-53153 | 5.7 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Ancillary Function Driver for WinSock | CVE-2025-53154 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Role: Windows Hyper-V | CVE-2025-53155 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Storage Port Driver | CVE-2025-53156 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Local Security Authority Subsystem Service (LSASS) | CVE-2025-53716 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Ancillary Function Driver for WinSock | CVE-2025-53718 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-53719 | 5.7 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2025-53720 | 8.0 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Connected Devices Platform Service | CVE-2025-53721 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Desktop Services | CVE-2025-53722 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Role: Windows Hyper-V | CVE-2025-53723 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Push Notifications | CVE-2025-53724 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Push Notifications | CVE-2025-53725 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows Push Notifications | CVE-2025-53726 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| SQL Server | CVE-2025-53727 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Dynamics 365 (on-premises) | CVE-2025-53728 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Azure File Sync | CVE-2025-53729 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Visio | CVE-2025-53730 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Microsoft Office | CVE-2025-53731 | 8.4 | CVSS:3.1/AV:L/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Microsoft Office | CVE-2025-53732 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Word | CVE-2025-53733 | 8.4 | CVSS:3.1/AV:L/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Visio | CVE-2025-53734 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2025-53735 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Word | CVE-2025-53736 | 6.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2025-53737 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Word | CVE-2025-53738 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Microsoft Office Excel | CVE-2025-53739 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office | CVE-2025-53740 | 8.4 | CVSS:3.1/AV:L/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2025-53741 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2025-53759 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office SharePoint | CVE-2025-53760 | 7.1 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:L/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office PowerPoint | CVE-2025-53761 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Azure Stack | CVE-2025-53765 | 4.4 | CVSS:3.1/AV:L/AC:L/PR:H/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows GDI+ | CVE-2025-53766 | 9.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Azure OpenAI | CVE-2025-53767 | 10.0 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:N/E:U/RL:O/RC:C | N/A | Yes | No | No |
| Windows Security App | CVE-2025-53769 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Web Deploy | CVE-2025-53772 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| GitHub Copilot and Visual Studio | CVE-2025-53773 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft 365 Copilot’s Business Chat | CVE-2025-53774 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:L/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows NTLM | CVE-2025-53778 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Kerberos | CVE-2025-53779 | 7.2 | CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H/E:F/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Azure Virtual Machines | CVE-2025-53781 | 7.7 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Teams | CVE-2025-53783 | 7.5 | CVSS:3.1/AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Word | CVE-2025-53784 | 8.4 | CVSS:3.1/AV:L/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Microsoft Exchange Server | CVE-2025-53786 | 8.0 | CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft 365 Copilot’s Business Chat | CVE-2025-53787 | 8.2 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:L/A:N/E:U/RL:O/RC:C | N/A | Yes | No | No |
| Windows Subsystem for Linux | CVE-2025-53788 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows StateRepository API | CVE-2025-53789 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Azure Portal | CVE-2025-53792 | 9.1 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:N/E:U/RL:O/RC:C | N/A | Yes | No | No |
| Azure Stack | CVE-2025-53793 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
Wir veröffentlichen erneut 8 CVEs, die nicht von Microsoft stammen:
| CNA | Tag | CVE | FAQs? | Workarounds? | Mitigations? |
|---|---|---|---|---|---|
| Chrome | Microsoft Edge (Chromium-based) | CVE-2025-8576 | Yes | No | No |
| Chrome | Microsoft Edge (Chromium-based) | CVE-2025-8577 | Yes | No | No |
| Chrome | Microsoft Edge (Chromium-based) | CVE-2025-8578 | Yes | No | No |
| Chrome | Microsoft Edge (Chromium-based) | CVE-2025-8579 | Yes | No | No |
| Chrome | Microsoft Edge (Chromium-based) | CVE-2025-8580 | Yes | No | No |
| Chrome | Microsoft Edge (Chromium-based) | CVE-2025-8581 | Yes | No | No |
| Chrome | Microsoft Edge (Chromium-based) | CVE-2025-8582 | Yes | No | No |
| Chrome | Microsoft Edge (Chromium-based) | CVE-2025-8583 | Yes | No | No |
Fachartikel
KI-Agenten als interne Sicherheitsrisiken: Was Experimente zeigen

MCP-Sicherheitsstudie: 555 Server mit riskanten Tool-Kombinationen identifiziert
SOX-Compliance in SAP: Anforderungen, IT-Kontrollen und der Weg zur Automatisierung

Irans Cyberoperationen vor „Epic Fury“: Gezielter Infrastrukturaufbau und Hacktivisten-Welle nach den Angriffen

Steuersaison als Angriffsfläche: Phishing-Kampagnen und Malware-Wellen im Überblick
Studien

Drucksicherheit bleibt in vielen KMU ein vernachlässigter Bereich
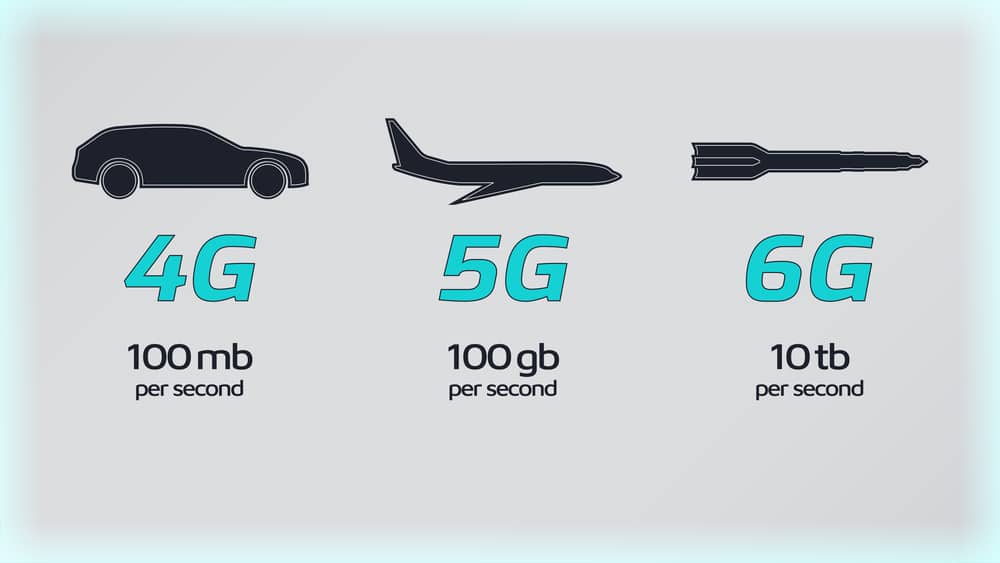
Sieben Regierungen einigen sich auf 6G-Sicherheitsrahmen

Lieferkettenkollaps und Internetausfall: Unternehmen rechnen mit dem Unwahrscheinlichen

KI als Werkzeug für schnelle, kostengünstige Cyberangriffe

KI beschleunigt Cyberangriffe: IBM X-Force warnt vor wachsenden Schwachstellen in Unternehmen
Whitepaper

Quantifizierung und Sicherheit mit modernster Quantentechnologie

KI-Betrug: Interpol warnt vor industrialisierter Finanzkriminalität – 4,5-fach profitabler

Cloudflare Threat Report 2026: Ransomware beginnt mit dem Login – KI und Botnetze treiben die Industrialisierung von Cyberangriffen
EBA-Folgebericht: Fortschritte bei IKT-Risikoaufsicht unter DORA – weitere Harmonisierung nötig

Böswillige KI-Nutzung erkennen und verhindern: Anthropics neuer Bedrohungsbericht mit Fallstudien
Hamsterrad-Rebell

Sichere Enterprise Browser und Application Delivery für moderne IT-Organisationen
Sicherer Remote-Zugriff (SRA) für Operational Technology (OT) und industrielle Steuerungs- und Produktionssysteme (ICS) – Teil 2
Incident Response Retainer – worauf sollte man achten?

KI‑basierte E‑Mail‑Angriffe: Einfach gestartet, kaum zu stoppen








