The European Union Agency for Cybersecurity issues technical guidance and recommendations on Electronic Identification and Trust Services helping Member States to implement the eIDAS regulation.
The European Union Agency for Cybersecurity (ENISA) completed a package of five reports in order to boost the implementation of the eIDAS regulation and promote the uptake of Electronic Identification and Trust Services. This work falls under the scope of the EU Cybersecurity strategy for the Digital Decade.
ENISA has been in the forefront of the developments on eIDAS since 2013 and with the Cybersecurity Act, established in 2019, the Agency has an extended mandate to support and assist the European Commission and the Member States in the area of electronic identification.
In this challenging period, the “EU digital ID scheme for online transactions across Europe” initiative will drive the revision of the eIDAS and will promote digital identities for all Europeans. ENISA in order to support the Commission has undertaken activities to explore the security considerations for trust service providers and remote identity proofing.
Four of the reports on trust services form an update of ENISA’s guidelines for qualified trust service providers. They represent a voluntary toolset designed to help those trust service providers comply with eIDAS. Specifically, they include:
- technical guidance on the security framework for Qualified Trust Service Providers (QTSP) and for the non-Qualified ones;
- security recommendations for Qualified Trust Service Providers based on Standards;
- guidelines on Conformity Assessment of Trust Service Providers.
A fifth report includes an analysis of the methods used to carry out identity proofing remotely and exploring security considerations. Remote identification allows customers to have their identification information collected and validated without the need for physical presence to the premises of the operator. This has become crucial during the COVID-19 pandemic as it allows access to cross-border online services offered by Member States.
EU Agency for Cybersecurity Executive Director, Juhan Lepassaar, stated: “Our lives today increasingly rely on online services. As a consequence, it is crucial we ensure the interoperability and security of electronic identification services across the EU, while simultaneously improving and expanding these services. Moving further towards a secure European Digital Identity will benefit both businesses and consumers in the Digital Market.’’
Technical Guidelines on Trust Services
ENISA issued the reports in order to update existing recommendations and guidelines issued in 2017 for qualified trust services. The purpose of these reports is therefore to focus on the requirements set by the eIDAS regulation and the emergence of new standards and new TSP services.
The new guidelines are presented in four different reports according to the following topics:
- trust service providers (qualified or not) looking for guidance on how to meet the requirements of the eIDAS Regulation;
- service providers seeking to clarify whether they qualify as a trust service provider according to the provisions under the eIDAS regulation;
- relying parties seeking to evaluate to what extent their trust service provider complies with the eIDAS requirements.
As a result, the set of recommendations include:
- Security Framework for Qualified Trust Service Providers and for Non-Qualified Trust Service Providers. These guidelines consider the greater potential variety encountered in non-qualified trust service providers;
- Security Recommendations for Qualified Trust Service Providers based on Standards, and Guidelines on Conformity Assessment of Trust Service Providers.
These guidelines have been consulted with and validated by experts in the eIDAS field from various sectors.
Analysis of Methods for performing Identity Proofing Remotely
Electronic identification under eIDAS constitutes a digital solution designed to provide proof of identity for citizens or organisations, in order to access online services or perform online transactions.
Specifically, alternatives are foreseen to physical presence for identity proofing in the context of issuing qualified certificates and in doing so paves the way for remote identity proofing. Other identification methods can also be used provided that they are recognised at national level. To that purpose, national authorities are intended to provide equivalent assurance in terms of reliability and the equivalent assurance shall be confirmed by a Conformity Assessment Body (CAB).
The report stresses the need for a harmonised adoption and cross-border recognition of remote identity proofing methods as those are the key elements for an extended use of digital services and for cross-border transactions within the internal market.
Questioned on their practices, 11 out of 27 European Supervisory Bodies stated that they already accepted methods for remote identity proofing. In the same way the eIDAS regulation has made it possible for trust service and electronic identification systems to use remote identity proofing, the fifth Anti-money Laundering Directive (AMLD5) has also introduced this technique in the financial sector.
This report provides an overview of the most common methods for identity proofing illustrated by practical examples received by the different stakeholders. It also presents the current legal/regulatory landscape and supporting standards at the international and EU level.
In addition, it gives an overview of the status quo in the EU Member States on their remote identity proofing laws, regulations and practices. The report also analyses the input received through questionnaires from different stakeholders which use, offer or evaluate identity proofing solutions. In particular, the contribution of 80 different stakeholders show the importance of this topic and is the object of a study currently being performed by ETSI special task force (STF) 588.
Read the full report here: Analysis of methods to carry out identity proofing remotely
Event announcement – save the date for the Trust Services Forum 2021
Together with the European Commission, ENISA will organise the Trust Service Forum on 21st September 2021. This edition takes place for the 7th year in 2021 following its inception in 2015. Collocated with D-TRUST/TUVIT CA Day on 22 September 2021, the event is to take place in Berlin, Germany, provided that the current travelling and gathering restrictions will be lifted by then. More information: Trust Services Forum – CA Day 2021
Background
The EU Agency for Cybersecurity has been at the forefront of the developments in eIDAS since 2013. The Agency has been supporting the European Commission and the Member States in the area of trust services in many ways, including but without being limited to the following:
- security recommendations for the implementation of trust services;
- mapping technical and regulatory requirements;
- promoting the deployment of qualified trust services across Europe;
- raising awareness for relying parties and end-users.
The EU Cybersecurity Act of 2019 has strengthened the Agency’s role is supporting the implementation of eIDAS.
Further Information
Electronic Identification and Trust Services for Electronic Transactions in the Internal Market (eIDAS)
16th Meeting of Article 19 Expert Group: Strengthening Security for e-Trust Services
Fachartikel

RC4-Deaktivierung – so müssen Sie jetzt handeln

Plattform-Engineering im Wandel: Was KI-Agenten wirklich verändern

KI-Agenten im Visier: Wie versteckte Web-Befehle autonome Systeme manipulieren

Island und AWS Security Hub: Kontrollierte KI-Nutzung und sicheres Surfen im Unternehmensumfeld

Wie das iOS-Exploit-Kit Coruna zum Werkzeug staatlicher und krimineller Akteure wurde
Studien
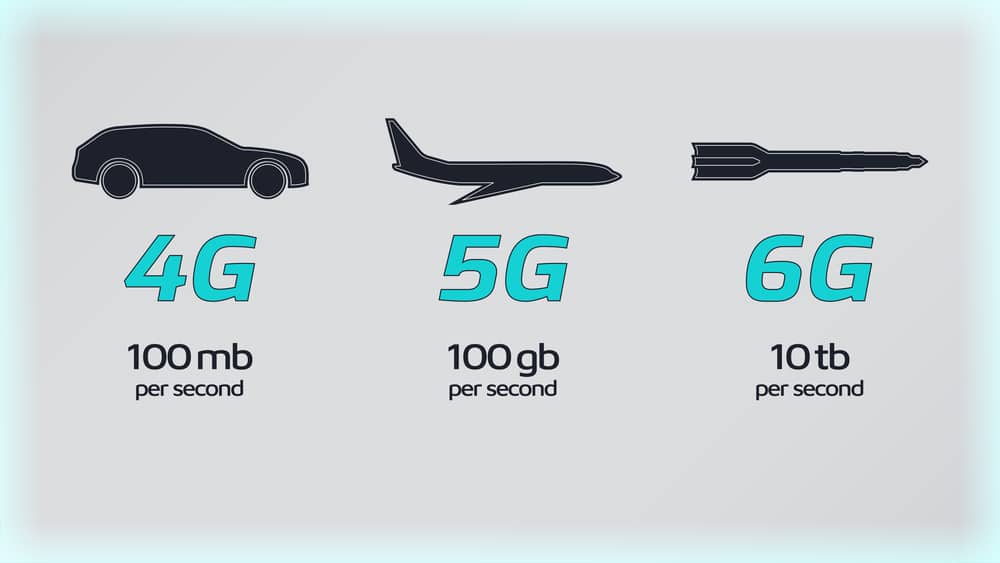
Sieben Regierungen einigen sich auf 6G-Sicherheitsrahmen

Lieferkettenkollaps und Internetausfall: Unternehmen rechnen mit dem Unwahrscheinlichen

KI als Werkzeug für schnelle, kostengünstige Cyberangriffe

KI beschleunigt Cyberangriffe: IBM X-Force warnt vor wachsenden Schwachstellen in Unternehmen
Finanzsektor unterschätzt Cyber-Risiken: Studie offenbart strukturelle Defizite in der IT-Sicherheit
Whitepaper

Cloudflare Threat Report 2026: Ransomware beginnt mit dem Login – KI und Botnetze treiben die Industrialisierung von Cyberangriffen
EBA-Folgebericht: Fortschritte bei IKT-Risikoaufsicht unter DORA – weitere Harmonisierung nötig

Böswillige KI-Nutzung erkennen und verhindern: Anthropics neuer Bedrohungsbericht mit Fallstudien

Third Party Risk Management – auch das Procurement benötigt technische Unterstützung

EU-Toolbox für IKT-Lieferkettensicherheit: Gemeinsamer Rahmen zur Risikominderung
Hamsterrad-Rebell
Sicherer Remote-Zugriff (SRA) für Operational Technology (OT) und industrielle Steuerungs- und Produktionssysteme (ICS) – Teil 2
Incident Response Retainer – worauf sollte man achten?

KI‑basierte E‑Mail‑Angriffe: Einfach gestartet, kaum zu stoppen

NIS2: „Zum Glück gezwungen“ – mit OKR-basiertem Vorgehen zum nachhaltigen Erfolg